Passwords are now the weakest link in many web apps, not because users are careless, but because phishing kits, credential stuffing, and token theft workflows have become highly automated. A passkey login implementation solves most of that pain by replacing shared secrets with phishing-resistant public key authentication. In this guide, you will build a production-ready WebAuthn flow with conditional UI autofill, device-bound credentials, and a practical recovery path that does not drag users back to insecure password resets.
Why passkeys are a better default in 2026
Passkeys (WebAuthn credentials synced securely by platform ecosystems) remove the reusable secret attackers love. Your server stores only a public key, while the private key stays with the user’s device or secure enclave. That gives you stronger sign-in with less friction for real users.
- Phishing resistance: credentials are scoped to origin, so fake domains fail.
- No password reuse risk: nothing reusable to leak from users.
- Better UX: biometric or device PIN unlock instead of typing.
If you are modernizing frontend auth flows, this pairs well with typed UI rollout patterns from our React feature flag guide: https://www.7tech.co.in/react-in-2026-build-a-typed-feature-flag-system-with-edge-config-and-progressive-delivery/.
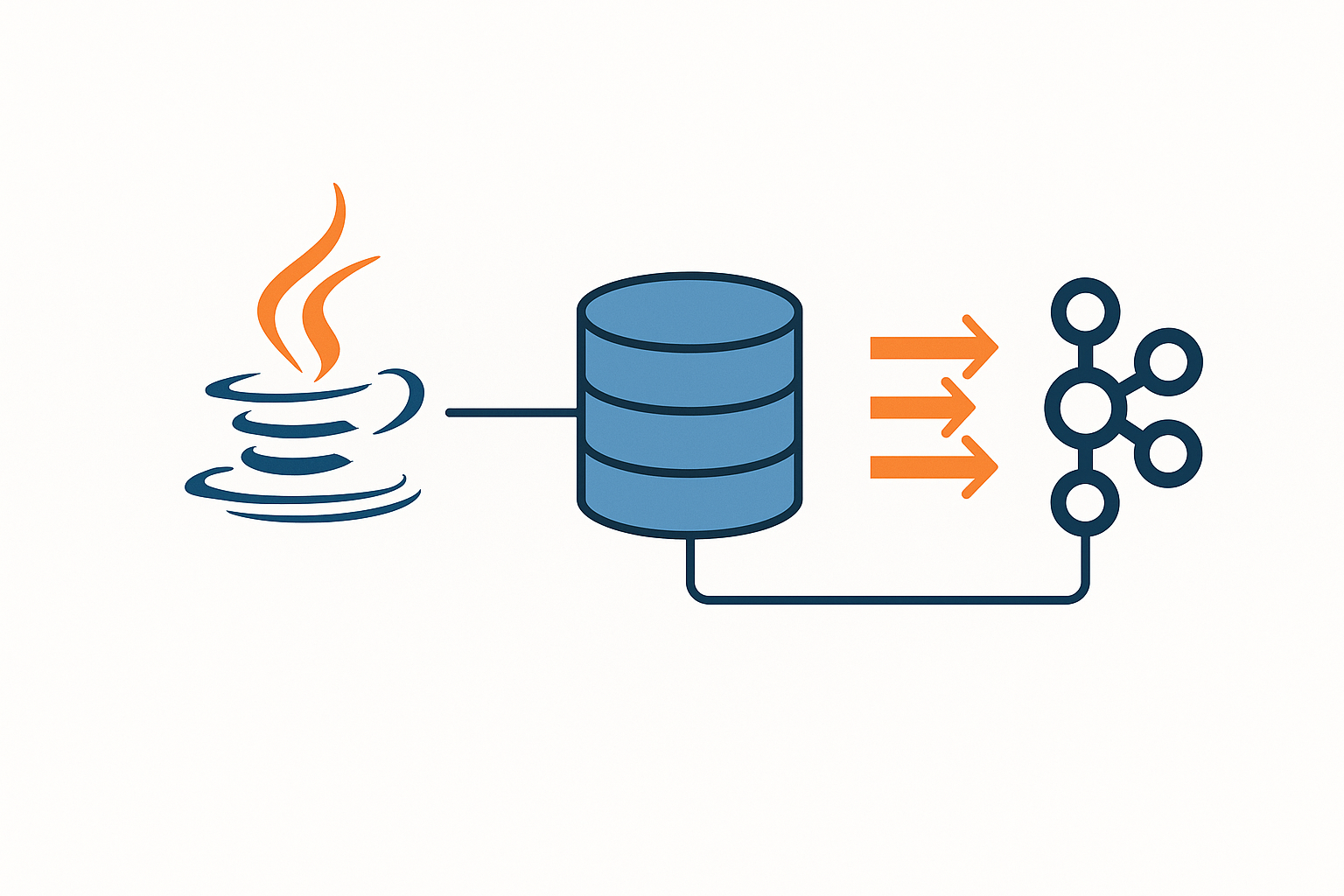
Architecture overview
Core components
- Browser: calls
navigator.credentials.create()andnavigator.credentials.get(). - Backend: creates challenge options, verifies attestation/assertion, stores credential public keys.
- Session layer: issues a normal app session cookie after successful assertion.
Data you should store
user_idcredential_id(binary/base64url)public_keysign_counttransports(optional but useful)created_at,last_used_at
Step 1: Registration (create a passkey)
Server generates a challenge and sends WebAuthn creation options. Keep challenge short-lived (for example 3-5 minutes), bind it to a nonce in server session state, and enforce the expected origin and RP ID during verification.
// Express-style pseudo endpoint: start registration
app.post('/auth/passkey/register/options', async (req, res) => {
const user = req.user;
const challenge = crypto.randomBytes(32).toString('base64url');
await saveChallenge({ userId: user.id, challenge, purpose: 'register', ttlSec: 300 });
res.json({
challenge,
rp: { name: '7Tech Demo', id: '7tech.co.in' },
user: {
id: Buffer.from(String(user.id)).toString('base64url'),
name: user.email,
displayName: user.name
},
pubKeyCredParams: [{ alg: -7, type: 'public-key' }, { alg: -257, type: 'public-key' }],
authenticatorSelection: {
residentKey: 'preferred',
userVerification: 'preferred'
},
timeout: 60000,
attestation: 'none'
});
});On the browser, call navigator.credentials.create() and post the result back for verification. After verification, persist the credential metadata.
Step 2: Login with conditional UI autofill
Conditional UI autofill lets returning users sign in from the browser’s account selector without typing username first. This reduces sign-in friction while keeping strong phishing resistance.
// Browser login with conditional mediation
const publicKey = await fetch('/auth/passkey/login/options', {
method: 'POST',
headers: { 'content-type': 'application/json' },
body: JSON.stringify({ emailHint: form.email?.value || null })
}).then(r => r.json());
const assertion = await navigator.credentials.get({
publicKey,
mediation: 'conditional'
});
await fetch('/auth/passkey/login/verify', {
method: 'POST',
headers: { 'content-type': 'application/json' },
body: JSON.stringify(assertion)
});Backend must verify:
- Challenge matches and is unexpired.
- Origin and RP ID hash are valid.
- Signature verifies against stored public key.
sign_countbehavior is consistent (handle zero counters per authenticator policy).
Step 3: Build account recovery without weakening security
The biggest deployment mistake is adding passkeys, then quietly allowing weak email-only reset flows. A safer recovery design uses layered trust:
- User proves mailbox control with short-lived link.
- Require a second factor: existing device approval, TOTP, or trusted recovery code.
- Apply cooldown for high-risk account changes (new passkey + payout actions).
- Notify all known channels on recovery and credential changes.
For threat-model alignment with modern replay defenses, see: https://www.7tech.co.in/cybersecurity-in-2026-stop-token-replay-in-spa-api-with-dpop-refresh-rotation-and-device-binding/.
Operational hardening checklist
Backend controls
- Store challenges server-side with strict TTL and one-time use.
- Use HTTPS everywhere and set secure, httpOnly, sameSite cookies.
- Rate-limit registration and assertion endpoints per IP and account.
- Log verification failures with reason codes, never raw credential blobs.
Frontend controls
- Feature-flag rollout by cohort first, then percentage.
- Graceful fallback for browsers lacking full WebAuthn UX support.
- Clear UI copy: “Use passkey”, “Use another method”, “Recover account”.
For production API stability under retries and traffic bursts, this authentication layer also benefits from patterns in our Node and Python reliability guides:
- https://www.7tech.co.in/node-js-in-2026-secure-your-backend-with-node-22-permissions-native-env-files-and-built-in-test-coverage/
- https://www.7tech.co.in/python-in-2026-build-a-production-ready-async-api-client-with-retries-rate-limits-and-typed-responses/
Common mistakes to avoid
- Storing challenges in client-side state only: enables replay tricks.
- Skipping RP ID/origin validation: breaks phishing resistance guarantees.
- No recovery drill: users get locked out during device loss incidents.
- No observability: you cannot distinguish UX drop-off from attack noise.
Conclusion
A well-designed passkey login implementation gives you stronger account security and a faster sign-in experience at the same time. The key is to treat WebAuthn as a full lifecycle system: robust registration, clean conditional sign-in UX, and hardened recovery. Roll it out gradually, monitor auth success and recovery abuse metrics, and you will phase out passwords without hurting real users.
FAQ
1) Are passkeys enough to replace passwords completely?
For many consumer and SaaS apps, yes, if you implement reliable recovery and cross-device support. Keep a temporary fallback during migration, then reduce it over time.
2) Does WebAuthn work only with biometrics?
No. Biometrics are one unlock method. Platform PIN or security keys also work depending on device and policy.
3) What is the most important verification check on the server?
Treat challenge validation, origin/RP ID checks, and signature verification as equally mandatory. Skipping any one of them weakens the security model.
Leave a Reply